Weak Session IDs
isSession Attribute
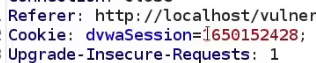
An example in DVWA, the isSession token is shown in intercepts on the weak sessionIDs vulnerability page. The page will set a new cookie called dvwaSession each time the button is clicked.
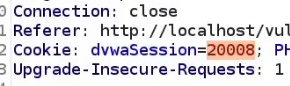
Clicking the generate button and intercepting the request shows the dvwaSession in the cookie. Note this is vulnerable as it's (very likely) not a random value.
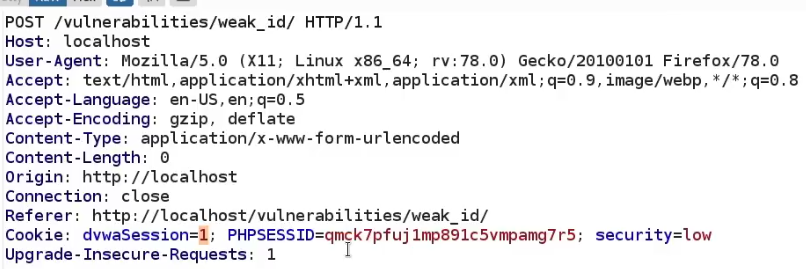
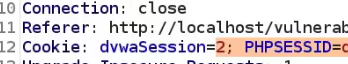
When we generate again, it generates 2, it's sequentially handled
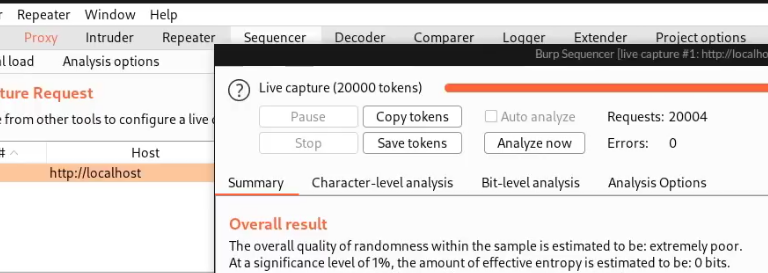
Now that we know this, we know that we can type in any number we want and impersonate that session. We can test this by sending it to the sequencer.
This vulnerability is verified in Burp's Sequencer.
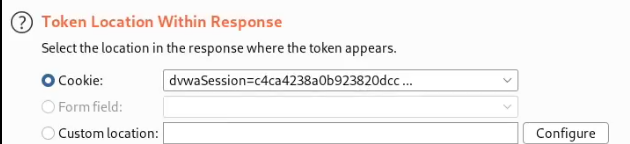
Note you may also need to show the token in Burp's response.
Medium security shows a more complex value, but still extremely short. The sequencer will show the same result.
High shows a much better value